
CPU vs GPU - What to choose to 'crack' passwords?
If we want to start the adventure with recovering passwords, e.g. from a handshake file during a WiFi network audit, zip files, encrypted documents, etc., it is worth doing it as efficiently as possible, as long as the hardware on which we work allows us.
For this purpose, I use a well-known and liked tool, as the creators themselves give "Swiss Army knife to recover passwords" - Hashcat. A common mistake of people starting their adventure with this topic is that Hashcat or other tools are run on virtual machines. This is not efficient because Hashcat has the ability to shift the calculations from the processor (CPU) to the card or graphics cards (GPU), which multiplies the speed and thus the efficiency of password recovery.Why isn't using virtual machines efficient?
Vbox or Vmware only emulate the graphics card and do not allow you to take full advantage of the hardware capabilities. And why is it worth switching calculations from CPU to GPU? The matter is simple: the weakest graphics card will always be more efficient than the most powerful processor. In the screenshots you can see the increase in GPU performance relative to the CPU on the same laptop with a Pentium i3 gen8 processor and an unimpressive GeForce card MX 150, except that the processor of cores involved in the calculations has 6, while this card model has 384 graphic cores in CUDA technology (the latest GPU cards of these cores have several thousand).
CPU:
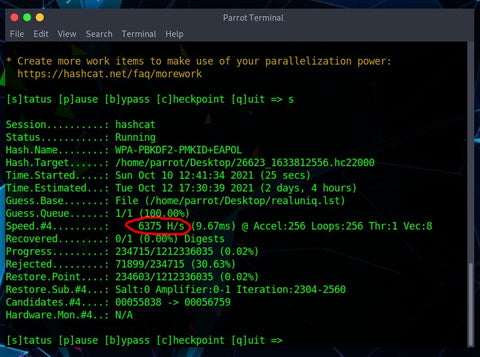
GPU:

To better illustrate the difference in time, I used a dictionary weighing 15.4 GB That is why it is worth using the full capabilities of Hashcat. If you want to have fun in this way, it is worth running a full Linux system, e.g. from a USB flash drive with presistence or from a disk. Hashcat is also available for Windows. Regardless of the system, we will have to install the latest drivers for our card. How to embrace it? I encourage you to read the documentation on the
project websiteAuthor of the entry - Rafał Sulikowski:
Rafał's Instagram: LINK
Instagram SAPSAN: LINK
Group on FB for Pentesters: LINK



Leave a comment